Data is dubbed as today's commercial currency, driving economies and business growth. It is therefore no surprise that cyber criminals are continually devising every means necessary to get to sensitive, confidential data.
The Cost of Data Breach
According to the breach level index, there are more than 6 million events of data loss or theft every day, and this number has been steadily increasing over the past years. This clearly shows that the magnitude of data lost and the need for enhanced data protection cannot be disregarded.
According to the "2018 Cost of a Data Breach" Study conducted by Ponemon Institute and sponsored by IBM Security, the global average cost of a data breach in 2018 amounted to $3.86 million, up 6.4% compared with 2017. Each stolen record containing sensitive and confidential information cost $148, a 4.8% increase year over year.
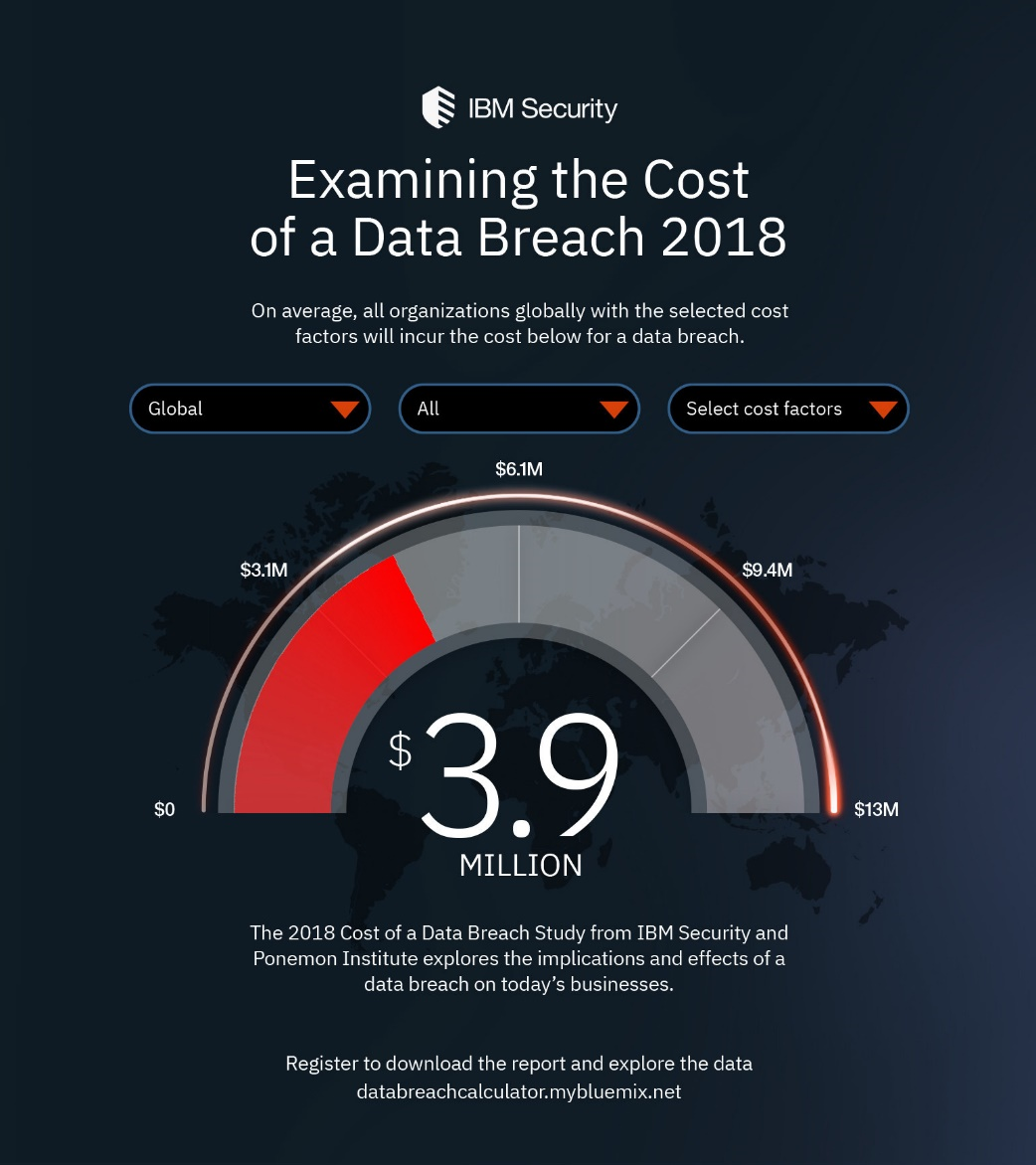
Image Source: IBM Security
These figures do not yet consider the hidden expenses that come with the full financial impact of a data breach, including but not limited to lost business, damaged reputation, cost of recovery, customer turnover, and more.
Types of Data Breaches
The Identity Theft Resource Center lists seven types of data breach categories:
- Insider Theft
- Hacking / Computer Intrusion (includes Phishing, Ransomware/Malware and Skimming)
- Data on the Move (systems, mobile devices or removal storage devices lost or stolen while in transit)
- Physical Theft
- Employee Error / Negligence / Improper Disposal / Lost
- Accidental Web/Internet Exposure
- Unauthorized Access
Flash Storage Vulnerabilities
In recent years, flash-based storage has steadily gained adoption in the industrial sector. Because flash has no moving parts, it delivers optimum performance and reliability while also enabling smaller, lighter, and power-efficient embedded systems.
The nature of flash, however, also makes it vulnerable to security challenges. Flash-based removable drives can easily be lost, misplaced or stolen, and embedded solid state drives (SSD)s or modules may be forcibly or illegally removed from host systems. Physical removal or loss of an unprotected device exposes data to the possibility that sensitive or confidential information may be accessed by an unauthorized party.
Aside from external adversarial threats, another major security challenge is the data disposal and erasure. When erasing data, flash storage devices have to delete an entire block made up of several pages containing data. To do this, valid data is moved elsewhere before the entire block can be erased. Frequently updated data is thus duplicated across the drive. Because of the constant moving of data to new locations, it is difficult to make sure that all stale copies (data marked for deletion) are completely removed. Besides, a certain portion of the device is used as a buffer for moving data around. This space, called over-provisioned space, is not accessible to the user. It is therefore likely that old versions or remnants of the "deleted" data could still remain in flash memory.
Simply "Deleting" data is often not enough, as it only removes the file's name from the directory or file table, and the user data remains until it is overwritten by new data. Also, there could be other folders where the data might still be located. In some devices, for example, "Deleting" files will just move them to the "Recently Deleted" folder, where they will stay for a good number of days. Even choosing to "Permanently Delete" data is not a fool-proof way to guarantee that the data cannot be reconstructed, as data recovery software suites can put back together what was already "permanently" deleted.
Securing Flash Storage
The Storage Networking Industry Association (SNIA), a non-profit global organization that develops standards to advance storage and information technology, addresses in its Data Protection Technical Whitepaper the need for relevant security controls to protect storage systems, infrastructure and data stored in them. The white paper also provides an overview of the ISO/IEC 27040:2015 (Information technology - Security techniques - Storage security) standard.
The document presents SNIA guidance on various facets of data security such as data confidentiality, classification, due diligence, retention and preservation, authenticity and integrity, monitoring/auditing/reporting, and data disposition/sanitization.
Data Confidentiality
According to ISO/IEC 27000, confidentiality refers to the "property of information that is not made available or disclosed to unauthorized individuals, entities or processors." Data confidentiality should apply to both data in flight (while it is being transferred) and at rest (stored within the storage device). Deemed the strongest means of ensuring data confidentiality is through cryptographic (encryption) mechanisms, where information is rendered garbled or indecipherable to unauthorized parties. Additional mechanisms such as authentication processes and authorization/access controls and data classification may also need to be implemented to guarantee confidentiality.
Data Disposition and Sanitization
Due to increasing concerns about privacy and security, electronic data disposal must be done with utmost care to minimize the risk of illegal/unauthorized access to information. The process of removing sensitive data from a storage device so it can no longer be recovered nor reconstructed is called "sanitization." Proper sanitization ensures confidentiality and enables organizations to have appropriate control over information that they are safeguarding.
There are many sanitization techniques available, however not all of them are optimized for the specific attributes of a NAND based storage media (as outlined above) but are rather based on magnetic and mechanical drives such as HDDs.
Software vs. Hardware Encryption
Software-based encryption is very commonly used, mainly for its low cost and ease of implementation across all devices in an organization. It is in fact available in major operating systems, but its strength largely depends on how secure the operating system is. If the operating system is compromised, so is the security provided by the encryption code.
Hardware-based encryption is free from the vulnerabilities of compromised software or operating systems, infection from malware, ransomware and other attacks and is thus considered more secure. And because it does not require host resources, CPU bandwidth is not utilized, hence there is no performance pay-off.
Solution – ATP’s SecurStor Feature Family
SecurStor is ATP’s answer to the growing data security concerns in the industry and is integrated into most of ATP’s new or upcoming industrial only flash storage solutions. Its feature set can be customized to the individual requirements of an application or a system and with that helps protect mission-critical applications against unauthorized access to data or systems.
SecurStor’s feature range includes, but goes far beyond, conventionally available data at rest protection mechanisms such as encryption or TCG Opal to assure protection not only of data that is stored in the NAND but also of data that is being processed inside a system or sent across a network.
For more information visit the ATP website or contact an ATP Representative or Distributor in your area.
