While cloud storage is increasingly becoming popular, industries continue to use local and removable storage such as memory cards. They are portable, handy and provide access to data on demand, in real time. Memory cards are available in different flash types and capacities to meet the needs of diverse applications as well as your organization’s budget, deliver robust performance, and offer excellent reliability for mission-critical data. As embedded systems continue to downsize, memory cards remain excellent storage choices due to their compact size and rich features.
Removable storage media such as microSD cards have numerous benefits, but they are also vulnerable to malicious attacks and unauthorized access. A misplaced or lost card, for example, can fall into the hands of someone who can access, manipulate, or tamper sensitive data, or inadvertently delete very important data. Memory cards are also vulnerable to malware attacks during firmware updates, where malicious code may be loaded to threaten or compromise an organization’s operations.
Thanks to advances in storage technologies, microSD cards now offer high levels of security without performance degradation. ATP Electronics recently introduced its self-encrypting SecurStor microSD cards with Secure Boot, hardware AES-256 XTS encryption, and customizable features to safeguard data from unauthorized access.
Self-Encrypting Drives
A self-encrypting drive (SED) is a type of storage device that automatically encrypts data even before it is stored on the drive. When the host is unlocked, data is also simultaneously decrypted. It requires no user input nor a separated software to perform the encryption or decryption.
The ATP SecurStor microSD card is an example of an SED with hardware-based full-disk encryption. This means that as soon as the microSD card leaves the ATP factory and inserted into a powered-on host, the data that is being written to and read from the microSD is automatically and constantly being encrypted and decrypted. The process is “transparent,” so neither the user nor the system application software is aware of it.
How do SEDs work? A unique random and symmetric data encryption key (DEK) is generated. This key is called the “AES key.” It is also AES encrypted, and the SED uses it to encrypt and decrypt data. AES stands for Advanced Encryption Standard, the first and only publicly accessible cipher approved by the US National Security Agency (NSA) for protecting top secret information. The numbers 256 represent the key length of 256 bits, which is the largest bit size and is practically unbreakable by brute force based on current computing power, making it the strongest encryption standard.
SEDs using AES-256 encryption will generate a 256-bit symmetric cipher key that is passed to the AES engine. The AES engine encrypts the plain text (source data) into cipher text (encrypted data) and sends it to the NAND flash storage.
Self-Encryption May Not Be Enough
While self-encryption provides high levels of security for data at rest (data already stored in the drive), it also has limitations – as soon as the SED is unlocked, it remains unlocked (and thus, accessible), until the host system where the drive is inserted is completely powered off. If the host system is just “asleep” or if it is being rebooted, the SED is still unlocked, thus exposing the stored data to malevolent parties.
SecurStor microSD Card: ATP’s Solution to Growing Security Needs
The ATP SecurStor microSD card goes beyond standard security features to provide iron-clad protection for data at rest.
Key Features:
- SecurEncrypt. This SED supports AES-256 XTS encryption of the User Data Area. It is the highest level of hardware encryption without performance trade-off. Here are important things to remember about this encryption standard:
- AES – a block cipher symmetric cryptographic algorithm.
- It uses a key of 256 bits and divides the data from the Sender in blocks of 128 bits each.
- XTS refers to the block cipher mode adopted by this specific algorithm to manipulate the Sender’s data, having a size higher than 128 blocks.
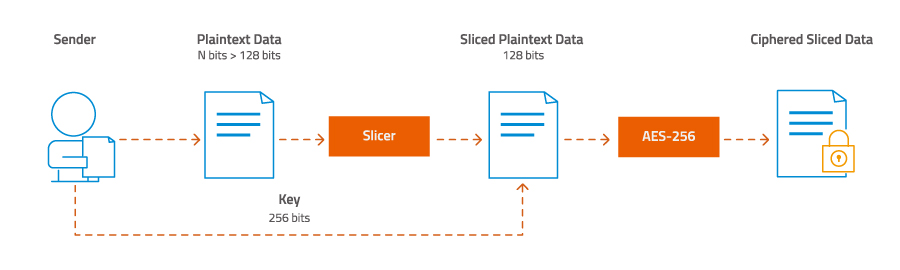
Figure 1. How AES-256 XTS encryption works
- Secure Erase. Deletes the AES encryption key to prevent unauthorized retrieval or recovery of the user data.
- Multi-Layer Authentication. Up to 10 user credential management on maximum of 4 different partitions.
- SecurBoot. Ensures the integrity and validity of the stored system’s BIOS configuration.
- Customization Option (per-project basis): Compliance with specific sanitization standards such as the US Air Force System Security Instruction (AFSSI) 5020.
Security Highlights:
- Max. partitions: 4
- Self-encryption with Hardware AES-256 XTS engine
- Customizable to comply with FIPS 140-2 Level 3 Security Policy (on per-project basis)
- Max. 10 individual user accounts with different privileges:
Normal (Read and Write), Read Only, Protected (read/write not allowed)
- User log-in history with time tag
- Secure Erase support (customization option available for US Air Force AFSSI-5020 compliance)
Product Highlights
ATP SecurStor microSD cards are available in multi-level cell (MLC) NAND flash, in capacities of 4 GB, 8 GB and 16 GB. Memory cards with 8 GB capacity are officially recommended as boot device for the Raspberry Pi OS (formerly, Raspbian).
Platform/OS Support and Customization Options*
- ATP SecurStor microSD cards support:
- x86 Windows 10 and Linux
- ARM Raspbian Linux
*Support for other operating systems may be available on request.
Customization Capabilities
ATP is fully capable of customizing security policies, as well as hardware, firmware, and software. For special requests, please contact the ATP sales representative in your area.
For more information on the ATP SecurStor microSD cards and other secure NAND flash storage products, visit the ATP website or contact an ATP Representative.